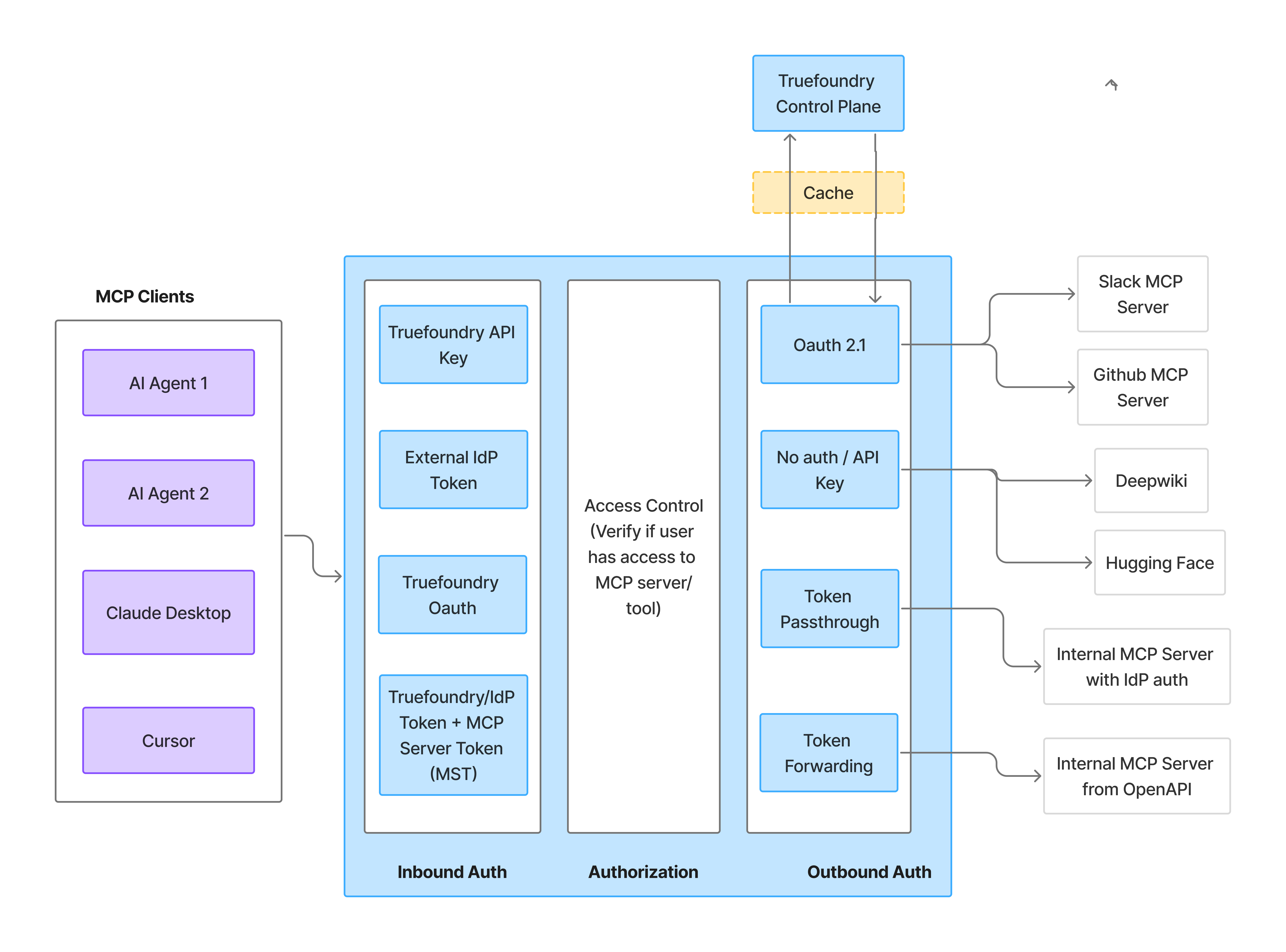
Authentication Architecture Overview
The Gateway provides a three-part authentication and authorization system:| Component | Description |
|---|---|
| Inbound Authentication | How clients (AI agents, developers, end users) authenticate to the Gateway |
| Access Control | Role-based policies determine which users can access which MCP servers and tools |
| Outbound Authentication | How the Gateway authenticates to downstream MCP servers |
| Question | What it determines |
|---|---|
| Who is calling the Gateway? | The Gateway Token — identifies the caller for inbound authentication |
| Whose credentials access the downstream service? | The MCP Server Auth — determines whose data and permissions are used at the upstream service |
Inbound Authentication
Access Control
Outbound Authentication
Inbound Authentication
Inbound authentication controls how clients authenticate to the Gateway. Any user or application requires valid credentials to talk to the Gateway, which allows the Gateway to identify the caller and apply authorization rules.When to use which method
| Method | When to use |
|---|---|
| TrueFoundry API Key (PAT) | Internal developers with TrueFoundry accounts |
| Virtual Account Token | Service-to-service callers and shared application tokens |
| Identity Provider Token | End customers or services authenticating with a JWT from your IdP (B2B SaaS, CIAM, service-to-service). See Identity Providers. |
| TrueFoundry OAuth | IDE tools (Cursor, VS Code) that need delegated user access |
Setup
Expand the method that matches your use case for the full setup steps and a code snippet.TrueFoundry API Key (Personal Access Token)
TrueFoundry API Key (Personal Access Token)
Virtual Account Token
Virtual Account Token
Identity Provider Token
Identity Provider Token
- B2B SaaS applications where your customers don’t have TrueFoundry accounts
- Applications that want to use their existing identity infrastructure
- Customer Identity and Access Management (CIAM) scenarios
- Service-to-service authentication where the caller already holds an IdP-issued JWT
Configure an Identity Provider
- Navigate to Settings > Security & Access > Identity Providers
- Click Add Identity Provider
- Fill in the form with the issuer URL, allowed audiences, and JWKS URI for your IdP (e.g., Okta, Azure AD)
- Choose whether validated tokens resolve to a virtual account (machine-to-machine callers) or a TrueFoundry user with team mapping (human users)
Add the Identity Provider mapping on the target
- For a virtual account, add an identity provider mapping that matches the configured Name Claim.
- For a team, add an identity provider mapping that matches the configured Team Claim, and ensure the target users exist in the tenant.
Grant MCP server access
- Navigate to the MCP server’s settings
- Go to Collaborators
- Add the mapped team, user, or virtual account with appropriate permissions
TrueFoundry OAuth
TrueFoundry OAuth
- Connecting to MCP servers from Cursor, VS Code, or other MCP-compatible IDEs
- Enabling team members to access MCP tools without sharing or managing API keys
- Leveraging existing TrueFoundry user authentication for MCP access
- The IDE prompts you to authenticate with TrueFoundry
- You sign in using your TrueFoundry credentials (or SSO if configured)
- TrueFoundry issues an OAuth token that the IDE uses for subsequent requests
- No manual token configuration is required
Access Control
Once authenticated, the Gateway verifies whether the user has permission to access the requested MCP server and tools.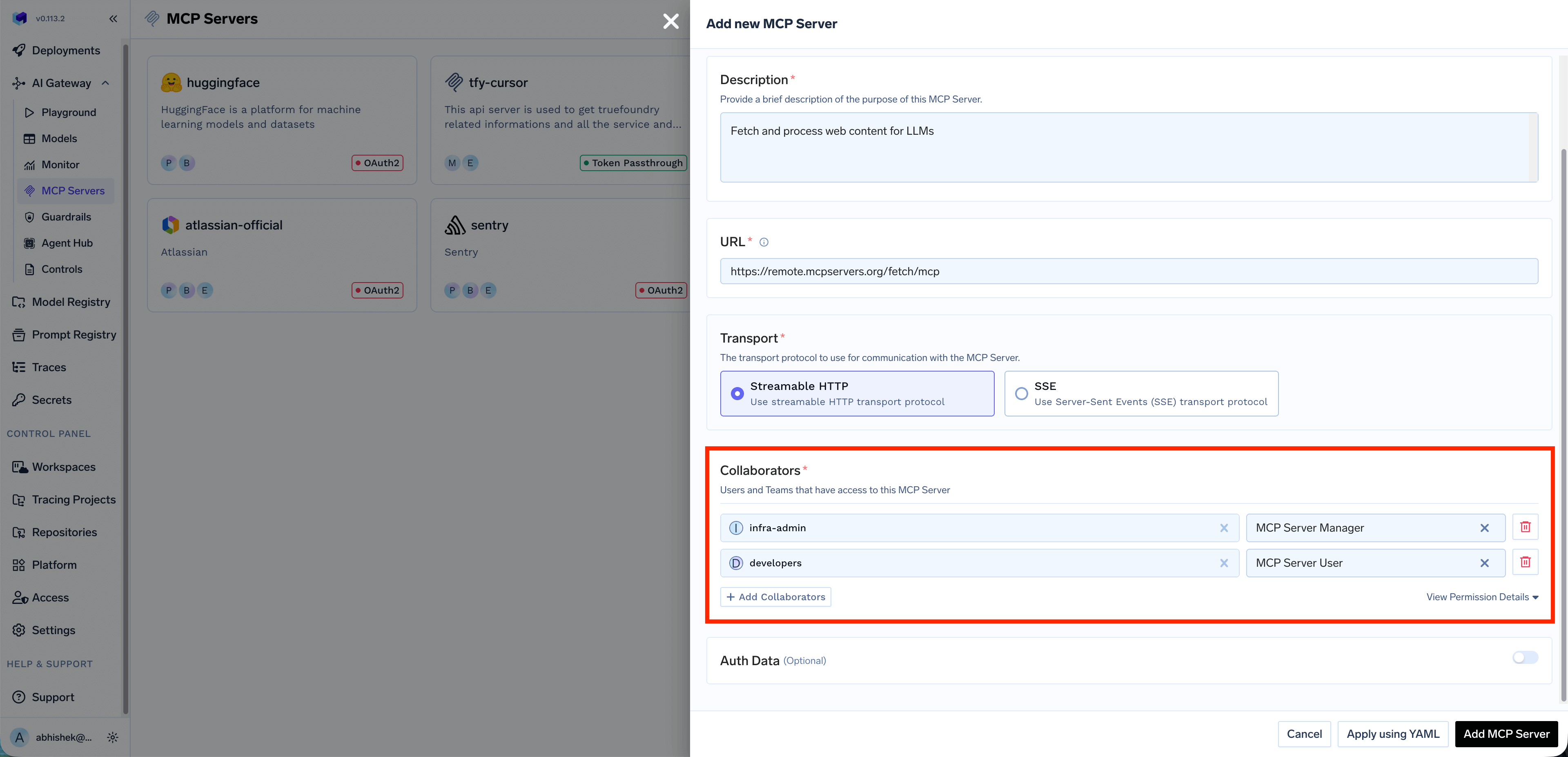
- Which MCP servers a user can access
- Which tools within an MCP server a user can invoke
Outbound Authentication
Outbound authentication controls how the Gateway authenticates to downstream MCP servers. TrueFoundry supports multiple authentication models to handle different MCP server requirements.When to use which method
| Method | When to use | Example MCP servers |
|---|---|---|
| OAuth2 (Authorization Code) | Per-user access to third-party services where each user authorizes their own account | Gmail, Slack, GitHub, Atlassian |
| OAuth2 (Client Credentials) | Server-to-server access with no user interaction | Backend microservices, internal analytics |
| API Key — Shared | Shared resources or public APIs where one credential serves all users | Hugging Face, DeepWiki |
| API Key — Individual | Per-user upstream API keys (each user provides their own via Auth Overrides) | Third-party per-user APIs |
| No Auth | Public APIs that require no authentication | Calculator, public DeepWiki |
| Token Passthrough | Internal MCP servers that validate your IdP tokens directly | Internal MCP server with IdP auth |
| Token Forwarding | MCP servers with their own auth systems where the client provides credentials via x-tfy-mcp-headers | Internal MCP server from OpenAPI |
Setup
Expand each model below for configuration details and example use cases.No Auth / API Key
No Auth / API Key
- Demo or sandbox APIs
- Public tools like a Calculator MCP Server or DeepWiki MCP server
- Shared Credentials: One key is used by everyone. You configure the credential once, and the Gateway injects it into every request regardless of which end user is calling.
- Individual Credentials: Each user provides their own key. Users must supply their own API key through Auth Overrides before they can use the MCP server. The Gateway injects the user-specific key into requests.
Bearer {{API_KEY}} placeholder. Each developer provides their API key via Auth Overrides, and the Gateway injects the correct key per user.OAuth2
OAuth2
Authorization Code
The Authorization Code flow is a user-facing flow where each end user is redirected to the provider (e.g., GitHub, Slack, Atlassian) to authorize access to their resources. The Gateway manages the full OAuth lifecycle — consent, token storage, and automatic refresh.How it works:- End user authenticates with the Gateway (using a TrueFoundry token or an Identity Provider token)
- End user attempts to call an MCP tool → Gateway returns an auth error with the authorization URL
- End user visits the URL and completes OAuth consent on the third-party service (e.g., GitHub)
- TrueFoundry stores the OAuth token for that end user
- Future requests automatically include the end user’s OAuth token
Client Credentials
The Client Credentials flow is a server-to-server flow where the Gateway authenticates to the downstream MCP server using a shared client ID and secret. No user interaction is required — the Gateway obtains an access token directly from the provider’s token endpoint.How it works:- The Gateway sends the client ID and secret to the provider’s token endpoint
- The provider returns an access token
- The Gateway uses this token to authenticate requests to the MCP server
- Tokens are automatically refreshed when they expire
Token Passthrough
Token Passthrough
- Your MCP server trusts the same IdP that authenticated the user to the Gateway
- The MCP server is configured to validate TrueFoundry tokens or your IdP’s JWTs
- You want the MCP server to make authorization decisions based on the user’s identity
- User authenticates to the Gateway with their token (TrueFoundry or IdP)
- Gateway validates the token and checks access control
- Gateway forwards the same token to the MCP server
- MCP server validates the token and processes the request
Token Forwarding (Custom Headers)
Token Forwarding (Custom Headers)
x-tfy-mcp-headers header. This is useful when the MCP server requires specific authentication tokens or metadata that are different from the Gateway authentication.When to use Token Forwarding:- The MCP server requires a specific token format that differs from Gateway authentication
- You need to pass additional metadata or authentication headers
- The client has direct credentials for the MCP server
- Client authenticates to the Gateway with TrueFoundry token or IdP token (inbound auth)
- Client includes
x-tfy-mcp-headerswith additional headers for the MCP server - Gateway validates the inbound token and checks access control
- Gateway forwards the custom headers to the MCP server
Quick Decision Guide
Now that you’ve seen the inbound and outbound auth options, use this flowchart to pick the combination that matches your agent. Each outcome below includes a starter code snippet you can copy.| Outcome | Gateway Token | MCP Server Auth |
|---|---|---|
| Virtual Account + Shared Credentials | Virtual Account | Static headers (configured once in UI). All users get the same access level. |
| TrueFoundry PAT + Per-User OAuth | User’s TrueFoundry API Key | Per-user OAuth; user completes consent once. |
| Identity Provider Token + Per-User OAuth | JWT from a configured Identity Provider | Per-user OAuth; user completes consent once. |
Starter code for each outcome
Scenario A: Agent acts on YOUR behalf (Service mode)
Scenario A: Agent acts on YOUR behalf (Service mode)
- An internal support bot that queries your company’s knowledge base
- A code assistant that uses a shared GitHub service account
- A data analysis agent that accesses shared analytics databases
| Token Type | What to use | Why |
|---|---|---|
| Gateway Token | Virtual Account token | Identifies your service/application |
| MCP Server Auth | Shared credentials (pre-configured) | All requests use the same service account |
Scenario B: Agent acts on USER'S behalf (Per-user mode)
Scenario B: Agent acts on USER'S behalf (Per-user mode)
- A productivity agent that accesses the user’s own Gmail, Slack, or Calendar
- A development assistant that accesses the user’s GitHub repositories
- A CRM agent that sees only what the logged-in user can see
| Token Type | What to use | Why |
|---|---|---|
| Gateway Token | User’s token (TrueFoundry PAT or Identity Provider JWT) | Identifies which user is making the request |
| MCP Server Auth | Per-user OAuth (managed by TrueFoundry) | Each user’s own credentials |
Scenario C: Hybrid — some tools shared, some per-user
Scenario C: Hybrid — some tools shared, some per-user
Implementation Recipes
Code patterns for common implementation needs. The Gateway uses standard MCP transports — install thefastmcp Python client to follow these examples.
Connecting to an MCP server
The MCP Gateway exposes each registered MCP server at a unique URL. You can copy each server’s URL from the TrueFoundry UI.Handling OAuth-protected MCP servers
When an MCP server is configured with OAuth2 and the user hasn’t completed the OAuth flow, the Gateway returns a401 HTTP error whose JSON body contains authorization_urls the user must visit.
Handling OAuth errors in code:
error.type set to "McpAuthRequiredError". The authorization_urls field is a dictionary keyed by server name, and each value is the URL the user must visit to complete the OAuth consent flow.Mixing OAuth and header-based MCP servers
A common question: “My agent uses Gmail (OAuth) and a web search API (header-based). Do I need to handle them differently?” Answer: No. The Gateway handles this for you.-
Configure each MCP server with its auth model in the UI:
- Gmail MCP Server → OAuth2
- Web Search MCP Server → Static Header (API key)
- In your code, pass ONE Gateway token:
- The Gateway handles auth per server:
| MCP Server | Auth Model | What the Gateway does |
|---|---|---|
| Web Search | Static Header | Injects pre-configured API key |
| Gmail | OAuth2 | Looks up user’s OAuth token, injects it |
| Calculator | No Auth | Passes request as-is |
Overriding auth with x-tfy-mcp-headers
If you need to override the default auth for a specific MCP server, use the x-tfy-mcp-headers header. This is the implementation of the Token Forwarding outbound auth model.
server-1). Copy the identifier from the UI since virtual MCP servers contain multiple remote MCP servers.Building a complete MCP-enabled agent
A reusable wrapper that handles connection, OAuth errors, and multiple MCP servers:End-to-End Authentication Scenarios
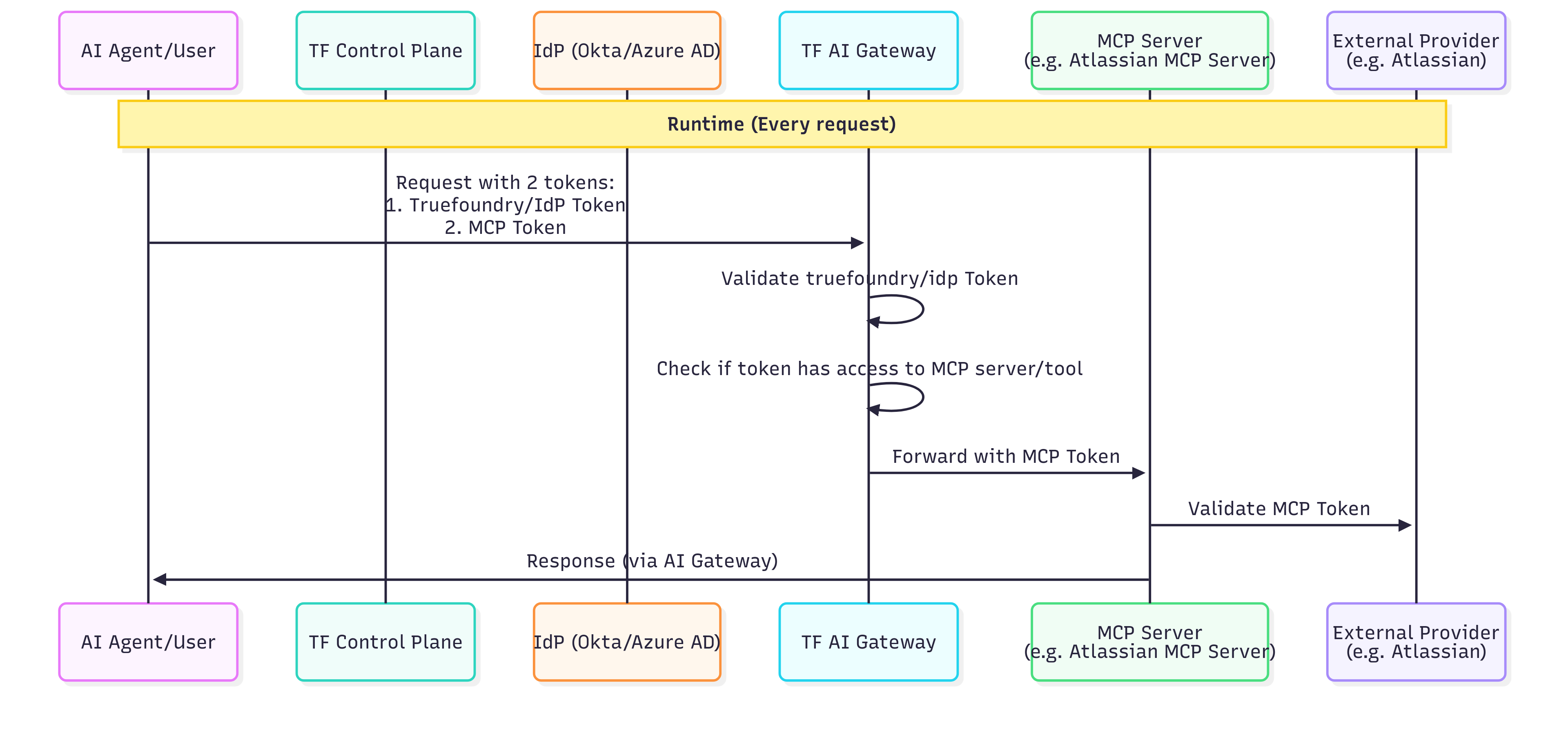
The accordions below show how inbound and outbound auth combinations work end-to-end, with sequence diagrams and step-by-step request flow tables. Most readers can skip this section unless they’re auditing the full request flow or implementing a less common combination.Scenario 1: TrueFoundry API Key + OAuth2 Outbound
Scenario 1: TrueFoundry API Key + OAuth2 Outbound
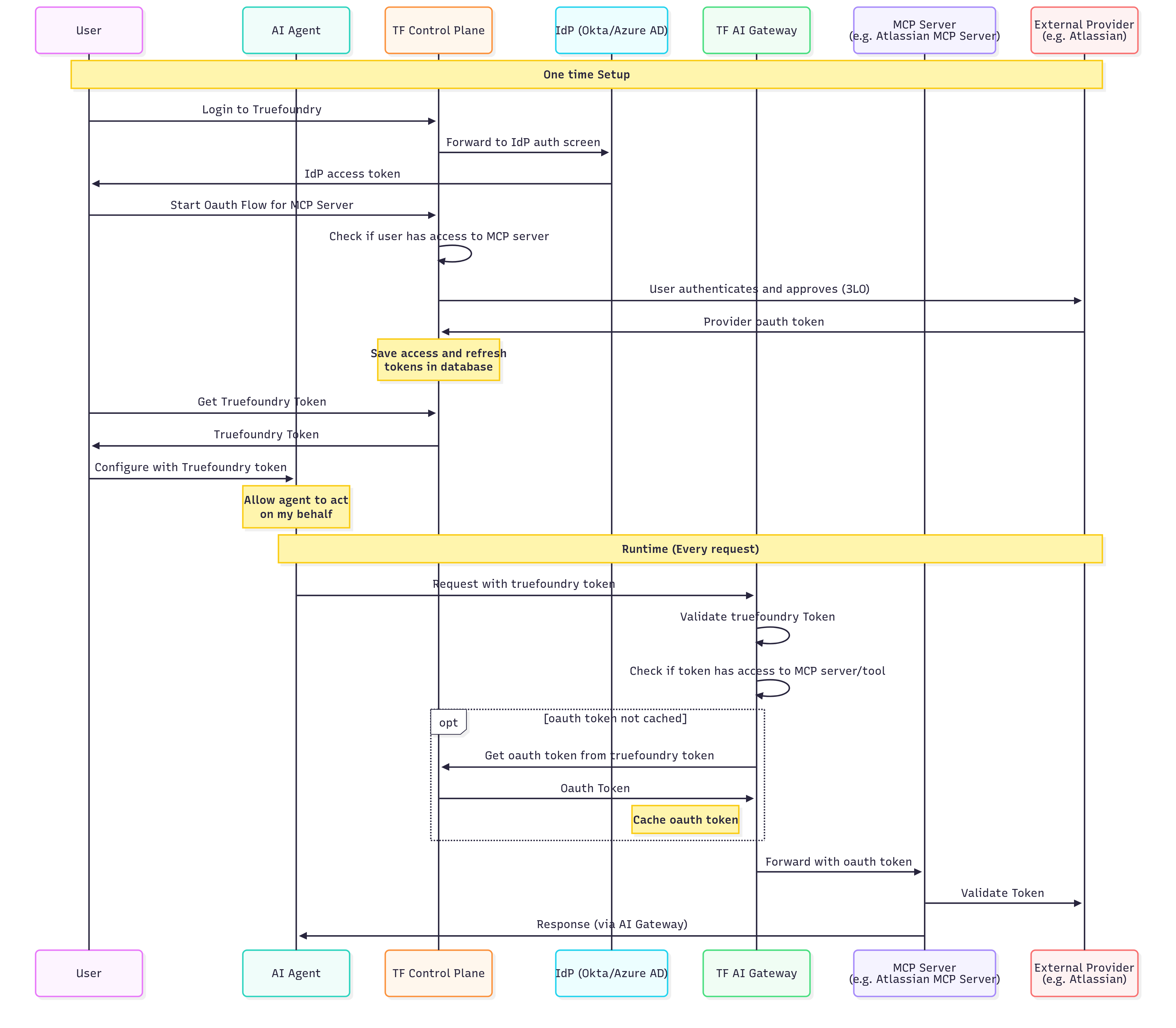
| Step | Action | Description |
|---|---|---|
| 1 | User → Control Plane | User logs into TrueFoundry |
| 2 | Control Plane → IdP | TrueFoundry redirects to your identity provider (Okta, Azure AD, etc.) |
| 3 | IdP → User | User authenticates and receives IdP access token |
| 4 | User → Control Plane | User initiates OAuth flow for the MCP server (e.g., “Connect to Atlassian”) |
| 5 | Control Plane | Verifies user has permission to access this MCP server |
| 6 | Control Plane → External Provider | User is redirected to the external service (e.g., Atlassian) to authorize access |
| 7 | External Provider → Control Plane | External service returns OAuth tokens after user approval |
| 8 | Control Plane | Securely stores access and refresh tokens, linked to the user’s identity |
| Step | Action | Description |
|---|---|---|
| 1 | Agent → Gateway | AI Agent sends request with TrueFoundry token (inbound auth) |
| 2 | Gateway | Validates the TrueFoundry token |
| 3 | Gateway | Checks if the token has access to the requested MCP server/tool |
| 4 | Gateway → Control Plane | (If not cached) Retrieves user’s OAuth token for this MCP server |
| 5 | Gateway | Caches the OAuth token for subsequent requests |
| 6 | Gateway → MCP Server | Forwards request with the user’s OAuth token (outbound auth) |
| 7 | MCP Server → External Provider | Validates token and fetches user-specific data |
| 8 | MCP Server → Agent | Returns response through the Gateway |
- Users authenticate once to TrueFoundry and access multiple OAuth-protected services
- Tokens are automatically refreshed when they expire
- Each user’s actions are attributed to their individual identity
- Users can revoke access to specific services at any time
Scenario 2: Identity Provider Token + OAuth2 Outbound (CIAM)
Scenario 2: Identity Provider Token + OAuth2 Outbound (CIAM)
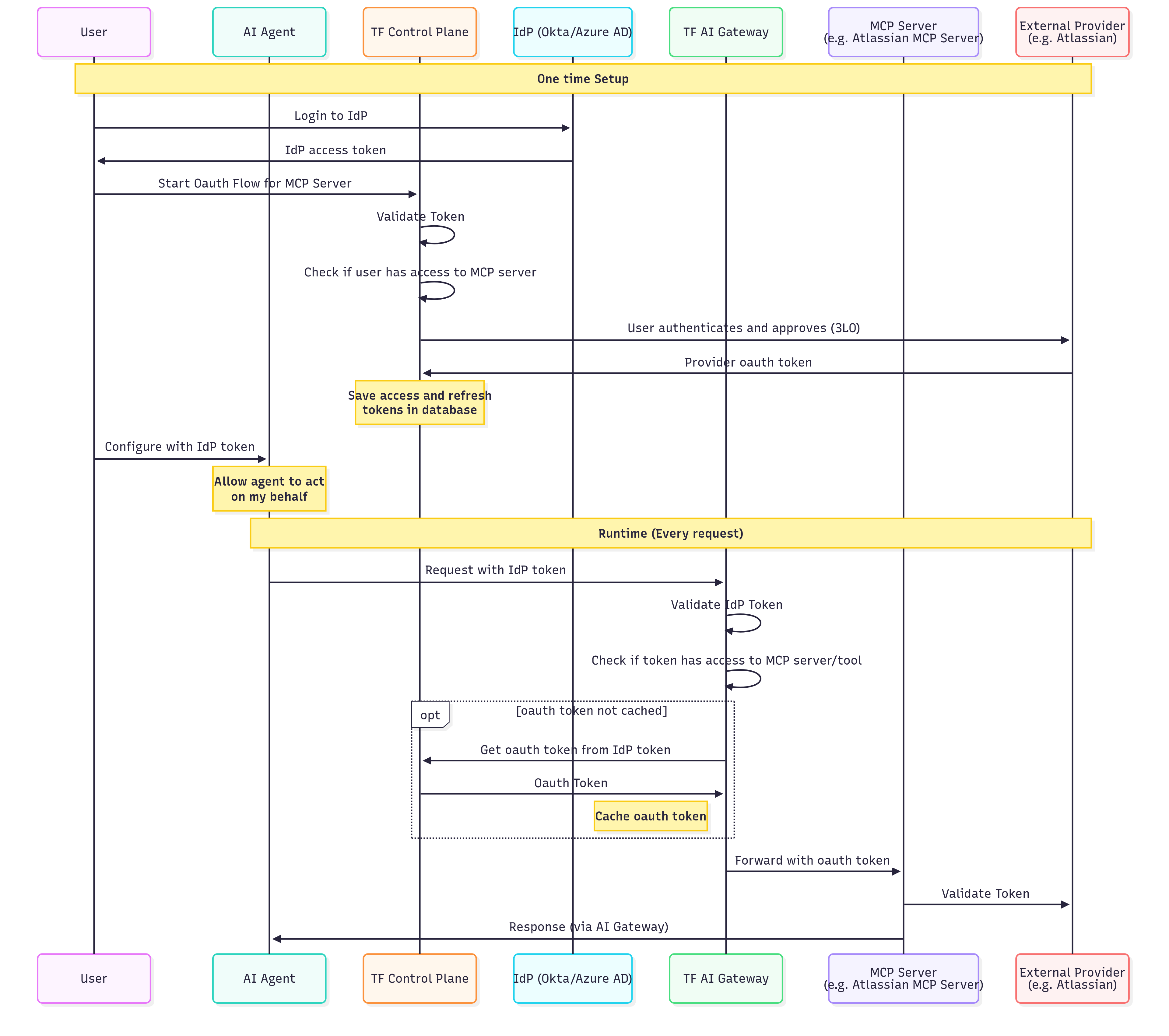
| Step | Action | Description |
|---|---|---|
| 1 | User → IdP | User logs into your identity provider directly (not TrueFoundry) |
| 2 | IdP → User | User receives IdP access token |
| 3 | User → Control Plane | User initiates OAuth flow for the MCP server |
| 4 | Control Plane | Validates the IdP token and extracts user identity (inbound auth) |
| 5 | Control Plane | Checks if the user/role has access to this MCP server |
| 6 | Control Plane → External Provider | Redirects user to authorize access (3-legged OAuth) |
| 7 | External Provider → Control Plane | Returns OAuth tokens; Control Plane stores them securely |
| Step | Action | Description |
|---|---|---|
| 1 | Agent → Gateway | AI Agent sends request with IdP token (inbound auth) |
| 2 | Gateway | Validates the IdP token using your SSO configuration |
| 3 | Gateway | Checks if the extracted user identity has access to the MCP server/tool |
| 4 | Gateway → Control Plane | (If not cached) Retrieves the user’s OAuth token using their IdP identity |
| 5 | Gateway | Caches the OAuth token for performance |
| 6 | Gateway → MCP Server | Forwards request with user’s OAuth token (outbound auth) |
| 7 | MCP Server → External Provider | Validates and processes the request |
| 8 | MCP Server → Agent | Returns response through the Gateway |
- Users authenticate with your IdP, not TrueFoundry (different inbound auth)
- The Gateway validates your IdP tokens directly
- Useful for B2B SaaS applications with end-customer integrations
Scenario 3: TrueFoundry/IdP Token + API Key Outbound
Scenario 3: TrueFoundry/IdP Token + API Key Outbound
| Step | Action | Description |
|---|---|---|
| 1 | Admin → Control Plane | Administrator registers the MCP server with static header authentication (outbound) |
| 2 | Admin | Configures the shared API key or bearer token in the MCP server settings |
| 3 | Admin | Defines which users/roles have access to this MCP server through RBAC policies |
| Step | Action | Description |
|---|---|---|
| 1 | Agent → Gateway | AI Agent sends request with user’s TrueFoundry or IdP token (inbound auth) |
| 2 | Gateway | Validates the user token |
| 3 | Gateway | Checks if the user has access to this MCP server (RBAC) |
| 4 | Gateway | Injects the shared credentials (static headers) into the request (outbound auth) |
| 5 | Gateway → MCP Server | Forwards request with shared service account credentials |
| 6 | MCP Server | Processes request using the shared credentials |
| 7 | MCP Server → Agent | Returns response through the Gateway |
- All users share the same level of access to the downstream service
- Actions cannot be attributed to individual users at the downstream service level
- TrueFoundry’s audit logs still track which user made each request at the Gateway level
Scenario 4: Token Passthrough (inbound token forwarded to MCP server)
Scenario 4: Token Passthrough (inbound token forwarded to MCP server)
| Step | Action | Description |
|---|---|---|
| 1 | Configure Inbound Auth | Set up TrueFoundry API key or Identity Provider token |
| 2 | Register MCP Server | Register the MCP server with Token Passthrough as outbound authentication |
| 3 | Configure MCP Server | Ensure the MCP server is configured to validate TrueFoundry tokens or your IdP’s JWTs |
| Step | Action | Description |
|---|---|---|
| 1 | User → IdP/TrueFoundry | User authenticates and receives a token |
| 2 | Agent → Gateway | AI Agent sends request with user’s token (inbound auth) |
| 3 | Gateway | Validates the token |
| 4 | Gateway | Checks if the user has access to this MCP server (RBAC) |
| 5 | Gateway → MCP Server | Forwards request with user’s token unchanged (outbound: token passthrough) |
| 6 | MCP Server | Validates the token and processes the request |
| 7 | MCP Server → Agent | Returns response through the Gateway |
- Your MCP server can validate TrueFoundry tokens or your IdP’s JWTs
- You want the MCP server to know the user’s identity
- The MCP server makes authorization decisions based on token claims
Scenario 5: Token Forwarding (Custom MCP Server Headers)
Scenario 5: Token Forwarding (Custom MCP Server Headers)
| Step | Action | Description |
|---|---|---|
| 1 | Configure Inbound Auth | Set up TrueFoundry API key or Identity Provider token |
| 2 | Register MCP Server | Register the MCP server (no outbound auth configured, or Token Forwarding mode) |
| 3 | Client Configuration | Client must include x-tfy-mcp-headers with MCP server credentials (see Overriding auth with x-tfy-mcp-headers) |
| Step | Action | Description |
|---|---|---|
| 1 | Agent → Gateway | AI Agent sends request with TrueFoundry/IdP token + x-tfy-mcp-headers |
| 2 | Gateway | Validates the inbound token |
| 3 | Gateway | Checks if the user has access to this MCP server (RBAC) |
| 4 | Gateway | Extracts headers from x-tfy-mcp-headers |
| 5 | Gateway → MCP Server | Forwards request with extracted headers (outbound auth) |
| 6 | MCP Server | Validates the custom headers and processes the request |
| 7 | MCP Server → Agent | Returns response through the Gateway |
- The MCP server has its own authentication system separate from Gateway authentication
- You need to pass user-specific tokens that the client manages
- The MCP server requires additional metadata alongside authentication
FAQ
OAuth2 vs Token Passthrough: which outbound auth should I choose?
OAuth2 vs Token Passthrough: which outbound auth should I choose?
| Question | If yes → |
|---|---|
| Does the MCP server connect to third-party services (GitHub, Slack, Google, etc.)? | OAuth2 (Authorization Code) |
| Is this a server-to-server flow with no user interaction? | OAuth2 (Client Credentials) |
| Does the MCP server validate the same token used for inbound auth? | Token Passthrough |
Token Passthrough vs Token Forwarding: what's the difference?
Token Passthrough vs Token Forwarding: what's the difference?
- Token Passthrough: The Gateway forwards the same token used for inbound authentication to the MCP server. The MCP server must be able to validate TrueFoundry tokens or your IdP tokens.
- Token Forwarding: The client provides separate credentials for the MCP server via
x-tfy-mcp-headers. These are different from the inbound auth token and are forwarded as-is to the MCP server.
Can I use multiple inbound auth methods for the same MCP server?
Can I use multiple inbound auth methods for the same MCP server?
Can I use a Virtual Account with OAuth-protected MCP servers?
Can I use a Virtual Account with OAuth-protected MCP servers?
- Use a TrueFoundry PAT or a JWT from a configured Identity Provider for per-user OAuth
- Configure the MCP server with Static Header (shared) auth instead
I'm getting 401 Unauthorized — what should I check?
I'm getting 401 Unauthorized — what should I check?
The tool I want to call says 'tool not found' — what now?
The tool I want to call says 'tool not found' — what now?
- List available tools using
client.list_tools()to confirm what’s exposed - Tool names are case-sensitive
- The MCP server may have been updated — refresh the tool list